Yesterday, my colleague Alexander Markov and I gave a brief presentation at Off The Ground Coffee at a cybercrime awareness micro-event organised by the local police force to help small businesses and individuals stay safe online.
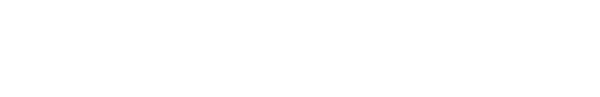
Our presentation focused on a particularly deceptive phishing attack, in which an e-mail masquerading as legitimate arrives pretending to be from Google:
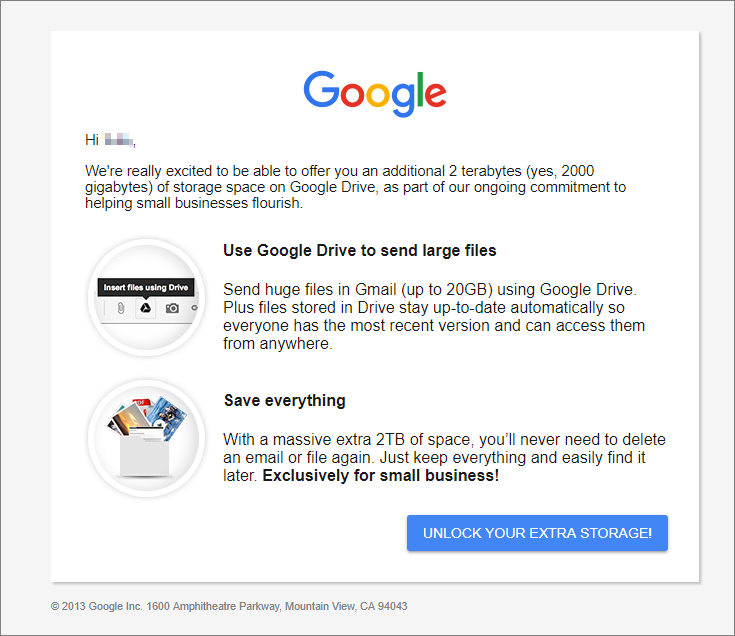
Clicking this button sends you to the legitimate Google sign-in page, but with a difference: behind the scenes, Google has been tricked into sending you somewhere else after you finish logging in:
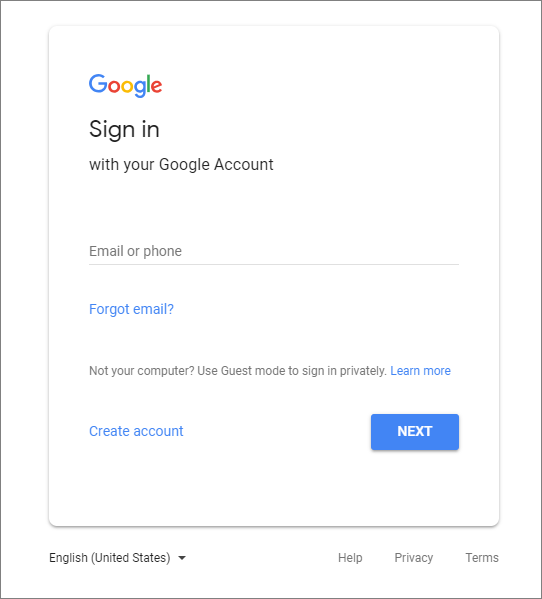
You log in and without even realising it, you're now on a webpage controlled by an attacker that has been crafted to look identical to the real website that asks you to 'confirm' your details:
Every button you press on this webpage, every movement your mouse makes, is being watched by an attacker. You don't even have to click 'submit' for me to get hold of your password (read more about that here). After clicking 'submit', the attacker has your information and whisks you along to a legitimate-looking 'congratulations' page:
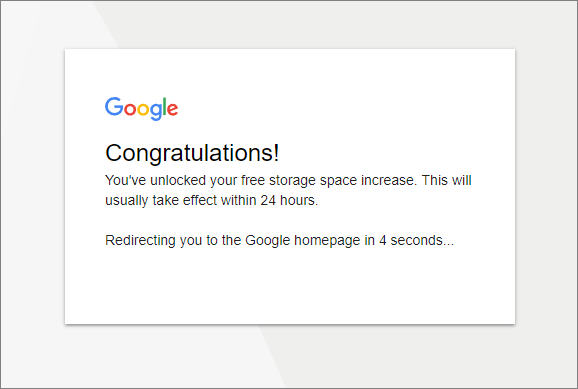
You're then redirected back to google.com, where you are of course signed in (remember, we went through the real login process).
Questions
Attendees had plenty of questions after we wrapped up the presentation, and I'll address some of the most common here:
Is this attack unique to Google?
No. Many websites can be tricked into sending you somewhere else without warning. This type of attack is called an "unvalidated redirect" or "unvalidated forward" and is relatively common. It occurs when the website's code does not check properly where it has been asked to send you on to. For example, google.com should never be asked to send you anywhere that is not also on google.com without warning you first. When an attacker finds a way around this, the problem arises.
Doesn't the green padlock in the corner protect me?
The little padlock in the corner of your web browser window is perhaps the most misunderstood little icon in the world. All it guarantees is that nobody is listening in the middle between you and the website you are visiting. You need to look at both the padlock and the URL (web address you're visiting) very carefully to make sure you're still on the website you expect to be on and that your computer's "conversation" with that website is private.
What can I do to keep myself safe from this attack?
This was by far the biggest concern among attendees, which is encouraging and shows a genuine recognition of the threat posed by cybercrime as well as a willingness to make adjustments to combat it. This warrants a blog post in itself, but to summarise:
-
Don't click links in e-mails unless you're certain you know you can trust them. Were you expecting this email? Even if it looks official, does it seem out-of-the-blue? If in any doubt whatsoever, reach out to the company's support department separately (don't follow a link from the e-mail!) to verify.
-
Use two-factor authentication. Every time you log in from a new computer, your phone will get a special code sent to it that you need to enter in order to continue. This way, if an attacker steals your password, they still can't access your account without also having your phone. Most major websites support this option.
-
Remain vigilant, and watch the URL. If you were on
google.comjust a moment ago but now you're somewhere else, stop. Did you expect to end up here? Were you warned that you were leavinggoogle.combefore you ended up here? Does this website look like Google? Might it be trying to trick you into thinking you're still there?
That's where I'll wrap it up today. Stay tuned for a more comprehensive set of tips on staying safe from phishing, how phishing attacks have evolved and the work we're doing towards making it easier to protect yourself.